On April 22, attackers hijacked @bitwarden/cli@2026.4.0 through a compromised GitHub Action. The malicious package was live for 90 minutes. In that window it harvested GitHub tokens, SSH keys, AWS credentials, npm tokens, shell history, and cloud configs.
That part is a familiar supply chain story. This part is not.
The malware had a target list. Not just credentials. Not just CI secrets. It explicitly hunted the configuration files of AI coding tools: Claude Code (~/.claude.json), Cursor, Codex CLI, Aider, and Kiro. MCP server config files were on the list too.
This is the first major supply chain attack that treated AI coding tool configs as a primary objective.
What the attack actually did
JFrog's analysis is the most complete technical breakdown. The malicious packaging layer was added on top of a legitimate Bitwarden CLI release. The root package.json advertised version 2026.4.0, but the embedded application metadata still referenced 2026.3.0 - a mismatch that confirmed the build pipeline was not used.
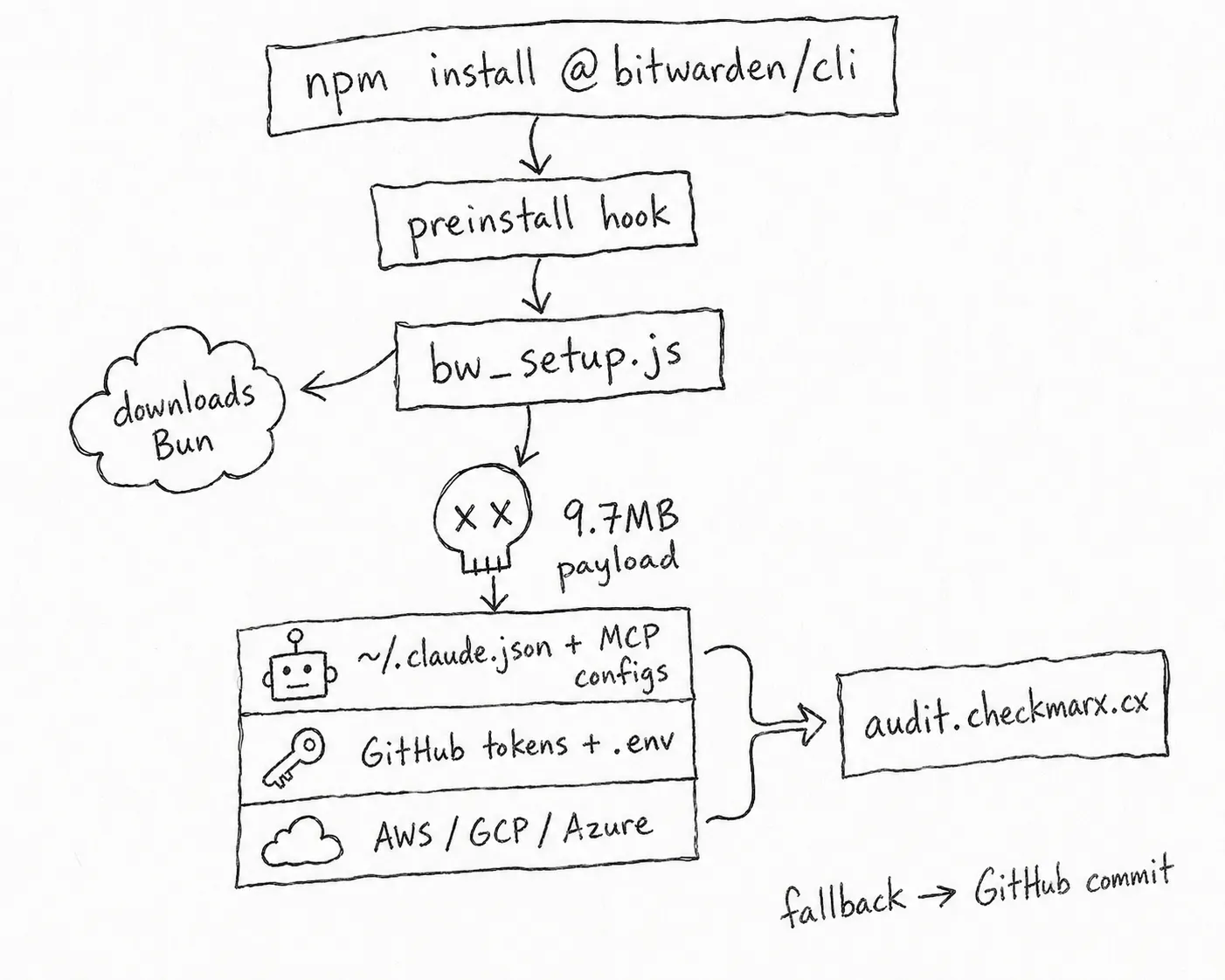
When a developer ran npm install @bitwarden/cli, the preinstall hook fired bw_setup.js. That loader downloaded the Bun JavaScript runtime from GitHub if it was not already present, then launched a 9.7 MB obfuscated payload.
Once deobfuscated, the payload ran in layers. First, a credential stealer targeting six surfaces: GitHub and npm tokens, SSH keys, environment variables, shell history, and cloud credentials across AWS, GCP, and Azure. Then, explicitly, AI coding tool configurations: ~/.claude.json, MCP server config files, and equivalent paths for Cursor, Codex CLI, Aider, and Kiro.
The stolen data was serialized, compressed with gzip, then encrypted in two layers: the AES key was encrypted with an embedded RSA public key using OAEP-SHA256, and the payload was encrypted with AES-256-GCM. The result was sent to audit.checkmarx.cx, a domain registered to impersonate Checkmarx so the outbound connection would blend into security telemetry. If that path failed, the malware committed the data to a GitHub repository as a fallback.
If GitHub tokens were found, the malware went further. It enumerated every repository the token could reach, injected malicious Actions workflows, and extracted CI/CD secrets from the resulting artifacts. StepSecurity put it plainly: "A single developer with @bitwarden/cli@2026.4.0 installed can become the entry point for a broader supply chain compromise, with the attacker gaining persistent workflow injection access to every CI/CD pipeline the developer's token can reach."
This is part of the TeamPCP campaign, running since March 2026. Previous targets: Trivy, Checkmarx KICS, LiteLLM, Axios. The attackers left a message in the code: a link to the Queen video "The Show Must Go On." This is the third wave of the same campaign. The Bitwarden CLI compromise is the first known attack to bypass npm's trusted publishing mechanism.
Bitwarden contained it in 90 minutes. The malicious version is gone from npm. The campaign is not over.
The same day: DPRK confirmed slopsquatting works
Today, April 29, researchers confirmed a separate attack that has been running since October 2025.
A package called @validate-sdk/v2 has been sitting on npm for seven months. It harvests secrets from compromised environments. It shows signs of being written with generative AI. It is linked to DPRK.
The reason it was found: Claude Opus hallucinated it as a dependency and added it to a project. The LLM invented a package name. An attacker registered it. The malware waited.
This is slopsquatting. The attack model: study which package names LLMs commonly hallucinate, register those names on npm, wait for an agent to install them. No phishing. No social engineering. No zero-day. Just patience and a hallucinated string.
A University of Texas / Virginia Tech / University of Oklahoma study found that 20% of 756,000 AI-generated code samples contained hallucinated package names. Aikido found a hallucinated package that spread to 237 repositories through forks before anyone noticed, downloaded daily by agents following skill instructions. The DPRK attack is the first confirmed case of an attacker weaponizing this in the wild.
Two attacks. One week. Both targeting the same surface.
Why AI coding tool configs are valuable
The reason attackers specifically target AI coding tool configs is the same reason those tools are useful: they have broad, persistent access.
Claude Code reads files, runs bash commands, calls APIs, writes to disk. It holds credentials in environment variables. It runs with the developer's full permissions. When you give an agent access to your codebase, you give it access to everything the developer can reach.
The config files contain more than settings. They contain session history, tool permissions, MCP server endpoints, and in some cases cached credentials. An attacker with your ~/.claude.json knows which MCP servers you are connected to, what tools you have approved, and what your agent has been doing.
The slopsquatting attack works because agents install packages without verifying the package is real. A human developer who has never heard of @validate-sdk/v2 would search for it, check the download count, look at the repository. An agent follows the instruction and runs npm install. The verification step does not exist.
Both attacks exploit the same gap: agents act with broad, persistent access and no mechanism to verify what they are touching.
What you can do now
There is no patch for slopsquatting. The DPRK package is gone. The next one is not registered yet. The Bitwarden package is gone. The next campaign target is not compromised yet.
What you can do is know what your agents have already done.
agent-strace audit-tools scans a repo for undeclared agent activity: tool calls, file writes, bash commands, package installs that do not appear in any approved session. If an agent installed something it was not supposed to, or touched a file outside its declared scope, it shows up.
agent-strace audit-tools --repo . --approved approved-tools.json
Given that the DPRK package has been live since October 2025, "already happened" is not a hypothetical. Run it.
Beyond detection, three things are worth doing now.
Rotate credentials that were in environment variables on any machine where @bitwarden/cli@2026.4.0 ran. The malware targeted environment variables. If you ran the compromised version, assume those credentials are known. Bitwarden's remediation steps and JFrog's indicators of compromise list what to check.
Audit your MCP server configs. The attack harvested ~/.claude.json and MCP-related files. Check .claude/settings.json, ~/.cursor/mcp.json, and equivalent paths for any MCP servers you do not recognize or did not add yourself. A rogue MCP server installed by malware looks identical to a legitimate one.
Pin package versions in agent-generated code. An agent that installs @validate-sdk/v2 because it hallucinated the name will do so regardless of what you tell it, unless the install step requires a version that exists in a lockfile. Pinning does not prevent hallucination but it prevents installation of a hallucinated package with no prior version history.
The structural problem
Detection and rotation are reactive. The structural problem is that agents hold long-lived credentials with broad scope.
The Bitwarden attack harvested credentials because they were sitting in environment variables, persistent and unscoped. A token that lives for the duration of one task and expires when the task ends cannot be harvested and reused. An agent that can only install packages from an approved list cannot be tricked into installing a hallucinated one.
These are authorization problems. The agent needs to operate with the minimum access required for the current task, and that access needs to expire when the task ends. This is not how most agent setups work today.
The Vercel breach in April started the same way: an AI tool held a broad, persistent OAuth grant. The tool was compromised. The grant became the door. The Microsoft Entra ID scope gap patched last week is the same pattern at enterprise scale. The MCP RCE flaw Anthropic called "expected behavior" is the same pattern at the protocol level.
The attacks are converging on the same root cause. Agents act with more access than they need, hold it longer than they should, and leave no record of what they did with it.
Start by looking at what your agents have already done.
agent-strace audit-tools --repo .
agent-trace is open source. Zero dependencies. Works with Claude Code, Cursor, Windsurf, and any MCP client.